Other cookies are configurable.
How to Use X (Twitter) in 2026: Privacy, Travel & Multi-Account Guide
X — the platform most of the world still calls Twitter — is the closest thing the internet has to a real-time public square. Breaking news lands here first, professional networks happen here in the open, niche communities organize themselves around hashtags, and entire careers are built on a few hundred well-aimed posts. By 2026, X has been through a rebrand, multiple algorithm rewrites, a contentious moderation pivot, and a paid-tier expansion — but the basic appeal has not changed: if something is happening anywhere in the world, somebody is posting about it on X within minutes.
What has changed is the privacy and access landscape around the platform. X collects more data than ever, monetizes it more aggressively, licenses tweets and DMs to AI training partners, and faces sporadic country-level blocks that take entire user bases offline overnight. This guide walks through how to actually use X in 2026 — the privacy settings most people never touch, the situations where a VPN saves you, the multi-account workflows that work, and the simple steps that keep your feed working from any network you connect to.
Why X is still the default real-time feed
For all the rebrands and policy chaos, X has held its position as the place breaking news, sports reactions, finance commentary, and political discussion happen first. Several specific properties keep it sticky.
- Open by default. Most accounts are public. You don’t need to follow someone to see what they post, which makes X a discovery engine in a way that closed networks like Facebook or LinkedIn aren’t.
- Real-time velocity. Posts surface in seconds, not minutes. For breaking-news, sports, market-moving events, and live commentary, X is unmatched.
- Communities form around hashtags and lists. #MedTwitter, #FinTwit, #NBATwitter — entire professional and fan communities self-organize without any central management.
- Long-form and video. Premium subscribers can post long articles and 4-hour videos. The platform has quietly absorbed parts of what blogs and YouTube used to handle.
- Spaces (live audio). Live audio rooms with thousands of listeners — useful for AMAs, panels, and breaking-news roundtables.
- API and bots, even after the cuts. Notification bots, news aggregators, market alerts — a substantial automation layer still runs on top of X, especially after the API tier changes settled.
The trade-off is privacy. The same openness that makes X useful as a public square also means everything you do on it is observable — by other users, by X itself, by advertisers, and increasingly by AI-training data buyers. Knowing what is and isn’t private is the first step to using X without surprises.
The privacy and access risks most people don’t notice
X is often described as “public anyway, so privacy doesn’t matter.” That mostly applies to your tweets — which are public by design. Everything around them is a different story.
DMs are NOT end-to-end encrypted by default
Direct Messages on X are encrypted in transit, but X holds the keys. End-to-end “Encrypted Chats” are limited to verified Premium users on both sides, and even then group DMs and media in encrypted chats have caveats. For sensitive conversations, treat regular DMs as readable by X.
Your IP is logged on every login
X stores the IP address of every login and most posts. Combined with your device fingerprint, that builds a precise timeline of where you posted from. On public Wi-Fi, the network can also see that you connected to X — even if it can’t see what you posted.
Tweets are licensed for AI training
X has openly licensed its data to AI training partners, including its own xAI and external customers. Anything you post becomes part of those data sets — usually without per-user consent. Private accounts are excluded, but anyone who gained access before you protected the account may have already cached your history.
Country blocks happen suddenly
X is fully or temporarily blocked in several countries. China, North Korea, Turkmenistan are constants. Pakistan, Brazil, Turkey, and others have hit X with country-wide blocks for days or weeks at a time, often with no warning. Without a VPN, a single trip or remote stint can mean losing X entirely.
None of this means X is unsafe. It means X is a normal cloud platform whose privacy and availability depend heavily on the network around it. Two changes — a VPN on top of the connection and a few account settings — close almost every gap a regular user actually faces.
How a VPN improves your X experience
A VPN does two things that matter for X. First, it wraps every connection your device makes inside an encrypted tunnel — so the local network and your ISP can no longer log that you used X, when, or for how long. Second, it replaces the IP address X sees with the IP of the VPN server you choose. That single change quietly fixes a long list of small problems.
Hides your real IP from X and the network
Every login record, every post, every DM you send carries the VPN server’s IP, not your home or carrier IP. Useful for privacy-conscious users, essential for journalists, activists, and anyone who posts on sensitive topics.
Encrypted traffic on every network
Cafe Wi-Fi, hotel networks, conference hotspots, and corporate guest Wi-Fi can no longer see which apps you connect to. Everything looks like a single encrypted tunnel to the VPN endpoint — including your X traffic.
Keeps X working in blocked countries
Pick a server in a country where X is available, and the platform works normally — both web and mobile app. This is routine for travelers heading to China, parts of the Middle East, and any country in the middle of an active block.
Cleaner separation for multiple accounts
If you run a personal and a brand account — or a public-facing and an alt account — routing each through a different VPN exit reduces X’s automated linking signals. Combined with separate browsers or browser containers, it’s a workable multi-account setup.
Not every VPN handles X well. A surprising number of services use exit IPs that X has already flagged as “datacenter abuse” ranges — tweets get rate-limited, login challenges multiply, and the experience deteriorates. The VPN you actually want for X is one with clean, frequently rotated exit IPs, fast servers (large image and video uploads need real bandwidth), and a no-logs policy.
Why simpler tools fall short
Before reaching for a VPN, a lot of users try lighter solutions. Most of them solve a smaller problem than they appear to.
X’s built-in “Protect your posts” setting
Locking your account hides your tweets from non-followers, but does nothing about IP logging, DM privacy, or country-level blocks. It also nukes your reach — useful for personal accounts, useless for anyone who actually wants to be seen.
Browser-based VPN extensions
Browser extensions only protect the X.com tab. They do nothing for the X mobile app on your phone, the third-party clients on your laptop, or the Spaces audio that uses different network paths. They also tend to use generic VPN protocols that captive portals and corporate firewalls already block.
Free VPNs from the app stores
Most free VPNs cap traffic at 300–500 MB per day. A single video upload to X eats half of that; a Spaces session eats the rest. Several free VPNs have also been caught logging traffic and selling browsing data — not really “free” in any meaningful sense.
Tor or random “privacy” tools
Tor works for the X website, but X aggressively rate-limits Tor exit nodes, login challenges multiply, and large media uploads are painfully slow. Random three-tap “privacy” apps usually wrap the same generic VPN protocols a free service already gives you, with extra ad SDKs.
Maximum VPN was built specifically as the “always-on” layer this list keeps pointing at: a device-wide tunnel with no traffic limits, a proprietary obfuscated protocol that captive portals and aggressive corporate firewalls do not recognize, and a no-logs policy. It costs nothing, supports up to 10 devices on one account, and runs in the background without nagging you for upgrades.
How to set up Maximum VPN for X
Setting Maximum VPN up does not require an account, an email address, or a payment method. The whole process happens inside Telegram and takes under a minute.
- Open the bot
Tap @MaximumVPN_official_bot in Telegram and press Start. There is no signup form — no email, no phone, no card. Need help with Telegram first? See our Telegram setup guide. - Get your personal configuration
The bot generates a unique connection key tied to your device and picks a nearby high-bandwidth server automatically. Configurations are available for Android, iOS, Windows, macOS, and Linux — pick the one matching the device you tweet from most. - Import the config into the app
Either copy the key or download the config file the bot sends you, then open it with the Maximum VPN app. The bot includes a step-by-step walkthrough with screenshots for each operating system.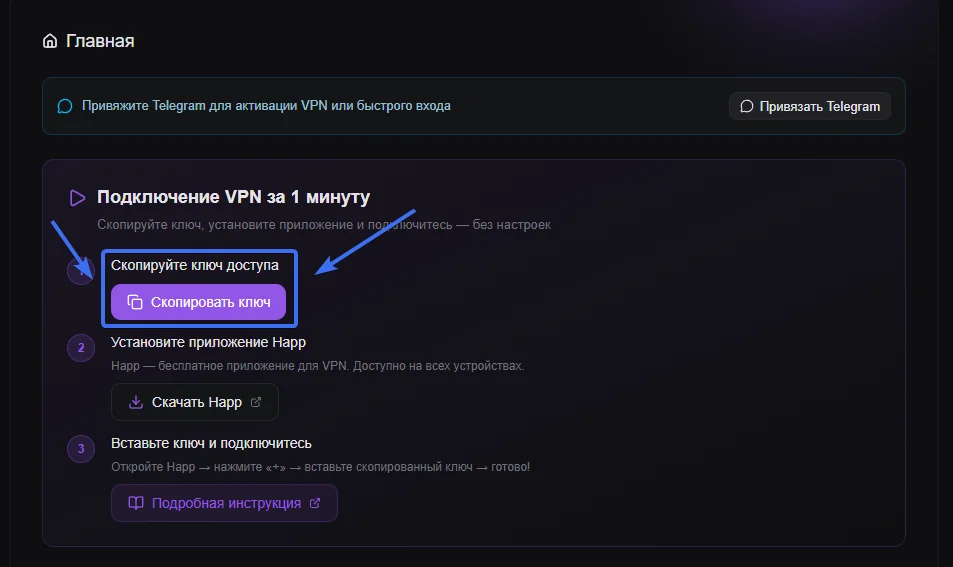
- Use X normally — only safer
Once the tunnel is up, open the X app or x.com. Posts send instantly, video uploads run at full speed, Spaces stays stable, and your real IP is hidden from the network and from X’s logs. The VPN runs in the background and does not affect the speed of other apps.
A few quick X settings worth turning on while you’re in there: enable two-factor authentication using an authenticator app, not SMS (Settings → Security and account access → Security → Two-factor authentication); turn off Personalize ads based on your activity (Settings → Privacy and safety → Ads preferences); review Data sharing with business partners and switch it off; and check Apps and sessions once a month to log out anything you don’t recognize. Five minutes, set once.
Why Maximum VPN is free
The fair question is why a service with this profile costs nothing. The honest answer is infrastructure. Maximum VPN runs on an automated server fleet that auto-scales capacity up and down with demand, retires under-used servers, and routes each user to the closest healthy node. That cuts the operating cost of a connection by an order of magnitude compared with a traditional VPN provider that has to keep large fixed pools of capacity online 24/7.
Beyond the infrastructure, the project is supported by voluntary donations from its community. That model is what lets us keep the service free, unlimited, and ad-free — no “upgrade for full speed” pop-ups, no “your trial expires in 7 days” tricks, and no quietly selling traffic data behind the scenes. Privacy is the product, not the bait.
Frequently asked questions
Is X (Twitter) safe to use in 2026?
X is generally safe but not private by default. Public posts are public, but DMs are NOT end-to-end encrypted unless both users have a Premium subscription and have opted into Encrypted Chats. Your IP is logged on every login, your device fingerprint is stored, and your activity feeds X’s advertising and AI-training data sets. A VPN closes the network-level side channels: encrypted traffic on public Wi-Fi, IP rotation, and protection against trivial scraping of who-talked-to-whom metadata.
Why do I get rate-limited or shadowbanned on X?
Most rate limits are tied to account behavior, not IP — fast posting, mass following, repeated mentions, automation. A VPN does not bypass account-level rate limits. Where a VPN does help: when X has flagged a specific public IP block (data centers, abused VPN exit nodes, certain mobile carriers) and is throttling everyone on it. Switching to a clean VPN endpoint can resolve those network-level slowdowns. For shadowban concerns, focus on account behavior first.
What is the best VPN for X (Twitter)?
The best VPN for X has clean (non-blacklisted) exit IPs, fast servers for media uploads, and a no-logs policy. Maximum VPN runs 70+ server locations, rotates IPs frequently to keep them unflagged, has no traffic limits — important for video uploads and Spaces — and is free with up to 10 devices per account.
Does X work in countries that block it?
X is fully or temporarily blocked in several countries, including China, North Korea, Turkmenistan, and at various times Pakistan, Brazil, Turkey, and parts of others. A VPN with a server in a country where X is available restores access — both the website and the mobile app. Maximum VPN’s obfuscated protocol is specifically designed to work on networks that block standard VPN protocols, which matters in countries with active censorship infrastructure.
Is using a VPN with X legal in the United States?
Yes. VPNs are fully legal in the United States and in most other countries. Using a VPN to protect your privacy on X, on public Wi-Fi, or while traveling is a standard security practice. X’s terms of service do not prohibit VPN use, though they may flag suspicious behavior patterns regardless of how you connect. A VPN does not legalize otherwise illegal behavior — local laws still apply.
Can I run multiple X accounts with a VPN?
Technically yes — a VPN can give different accounts different exit IPs, which helps avoid X’s automated duplicate-account detection. But X also uses device fingerprinting (browser, screen size, fonts, time zone, cookies), so a VPN alone is not enough. Use separate browsers or browser containers per account, clear cookies between sessions, and rotate VPN servers. Note that multi-accounting in violation of X’s terms can still get accounts suspended — a VPN does not change that.
X — private, anywhere
Set up Maximum VPN in under a minute. Free, no signup, no traffic caps. Post, scroll, and DM safely from any network — including the ones that try to block X entirely.
Get Maximum VPN free